A program uses three global integer variables HH, MM and SS to represent the current time in hours, minutes and seconds using the 24-hour clock notation.
Midnight would be represented as 00:00:00 (HH:MM:SS). If the variables HH, MM and SS contained the values 16, 30 and 10 respectively, then the time would be 16:30:10 or just after 4.30 in the afternoon.
A procedure Tick() will be called every second.
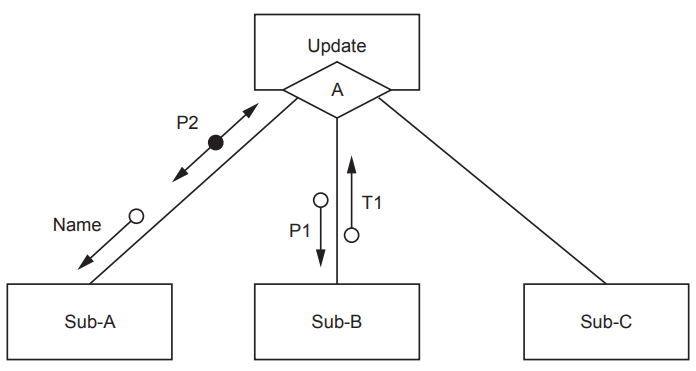
The procedure Tick() will:
update the value in
SSeach time it is calledupdate the values in
HHandMMas appropriatecall a procedure
CheckAlarm()at the start of each minutecall a procedure
NewDay()whenever the time reaches midnight.
Complete the pseudocode for procedure Tick().
PROCEDURE Tick()
Was this exam question helpful?