Resolving Non-Violent Forms of Conflict (DP IB Global Politics: HL): Revision Note
Cyber conflict
Cyber conflict is use of digital tools and technology by states or non-state actors to attack, disrupt or undermine the computer systems, infrastructure or information of an opponent in order to gain a political or strategic advantage
The purpose of cyber conflict can be to gain information, cause economic chaos or extort money
Although cyber conflict takes place online, it impacts the physical world significantly and is challenging to resolve
This type of conflict is asymmetric, meaning even small groups with limited resources can attack more traditionally powerful states, companies or actors
Actors often responsible for cyber conflict
Actor | Explanation |
|---|---|
States (often by using a third party) |
|
Terrorist groups |
|
Criminal gangs |
|
Hacktivists |
|
Challenges to resolving cyber conflict
It is not always clear who is behind the attack(s) as the the attackers often take elaborate measures to disguise their identity or are working on behalf of state actors
If the opponent is unclear, traditional conflict resolution strategies simply do not work
Cyberconflict is said to be a “grey zone” of conflict meaning it causes great damage but is not violent and consequences are not always immediately visible
The focus for most governments and companies is on preventing cyberwarfare by strengthening their operating systems because once the attack(s) have occurred the damage is done
Multiple actors including states, IGOS (e.g. UN, World Bank), Technology companies and Informal Forums (World Economic Forum), are looking at ways the global community work together to both prevent and immediately respond to these kinds of attacks, and better identify those responsible
Case Study
NotPetya (2017)
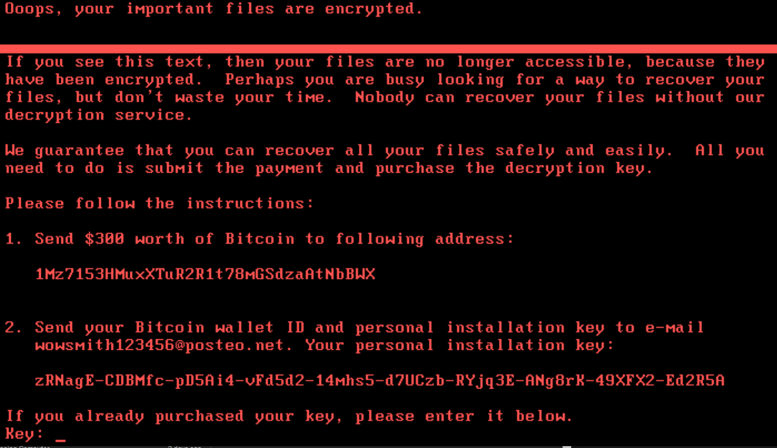
In June 2017, a cyberattack named NotPetya spread through global computer networks, causing an estimated $10 billion in damage — making it one of the most destructive cyberattacks in history
Although it appeared to be ransomware, it was designed purely to destroy data, with no possibility of recovery
What happened?
The attack was hidden inside a routine software update for a Ukrainian accounting programme
Once downloaded, it spread automatically, permanently deleting files
Ukraine was the primary target, but the malware spread globally, crippling shipping giant Maersk ($300m in losses), pharmaceutical company Merck ($870m), and disrupting NHS hospitals in the UK
Who was responsible?
The attack was attributed by the US, UK, and EU governments to Sandworm, a unit of Russian military intelligence (the GRU), amid ongoing tensions following Russia's annexation of Crimea
Russia denied involvement — a clear example of a state using a third party and plausible deniability to disguise its role
Links to key concepts
NotPetya illustrates several key features of cyber conflict
Its physical-world impact was enormous despite no conventional weapons being used
Its asymmetric nature meant a small group caused damage on a massive scale
Its grey zone character — destructive but not technically an act of war — meant no legal consequences followed
The absence of a binding global framework left affected states and companies with no meaningful avenue for accountability
Conflict with marginalised, vulnerable or most affected groups and individuals
Conflicts of this type arise when certain groups within society, such as ethnic minorities, women, people with disabilities, Indigenous communities or those living in poverty, face systematic disadvantage, discrimination or exclusion
This kind of conflict is closely linked to Galtung's theory of cultural violence
Deeply embedded social norms, beliefs and institutions legitimise the unequal treatment of certain groups, often making the conflict invisible to those not directly affected
Those outside marginalised or vulnerable groups are frequently unaware of, or indifferent to, these conflicts, as they do not experience the same barriers or harm
Resolving these conflicts requires multiple actors working together towards changes in social norms and institutional discrimination — each with different responsibilities and methods
Actors and strategies for resolution
Actor | Responsibilities and methods |
|---|---|
IGOs |
|
State governments |
|
NGOs and civil society |
|
Social movements |
|
Private companies |
|
Why these conflicts are difficult to resolve
Conflicts involving marginalised groups are particularly hard to resolve because the causes are often deeply embedded in culture, history and institutions rather than in a single identifiable event or actor
Galtung's concept of cultural violence helps explain why
When discrimination is normalised — through language, religion, media, or tradition — it can persist even after formal legal protections are introduced
Progress also depends on political will, which is often lacking when those in power are not directly affected
Different actors may have conflicting priorities or move at very different speeds, and meaningful change typically requires sustained effort across generations rather than a single intervention

Unlock more, it's free!
Was this revision note helpful?
