Technology (DP IB Global Politics: HL): Revision Note
Technology in global politics
A set of topic areas is presented for the study of global political challenges to facilitate your explorations. These should not be seen as fully discrete or disconnected topics, but rather as overlapping areas of study that can contribute to understanding and addressing global challenges.
You can conduct an in-depth study of two of the topic areas—for example, security and health—or you may choose to explore the interconnections of multiple topic areas based on a selected case study.
Technology has transformed how political actors communicate, organise, exercise power and wage conflict
The political implications of technology are far-reaching — affecting governance, warfare, human rights, development and social organisation
Technology is both a tool for political actors and a site of political contestation in itself
Why is technology a global political challenge?
Technology develops faster than the political and legal frameworks designed to govern it, creating significant regulatory gaps
Technology concentrates power in the hands of those who control it
States with advanced cyber capabilities and large technology corporations can exercise enormous influence over others
The benefits and risks of technology are distributed unequally
The digital divide excludes some populations from the benefits of digital technology while leaving them exposed to its political consequences
Technology challenges traditional concepts of sovereignty
Cyberattacks cross borders without physical intrusion; information spreads globally regardless of national censorship
Technology is dual-use
The same tools can empower citizens and oppress them, enable development and accelerate environmental harm, facilitate communication and spread disinformation
Key terms and concepts
Term | Definition |
|---|---|
Cyberattack |
|
Cyberwarfare |
|
Disinformation |
|
Misinformation |
|
Artificial intelligence (AI) |
|
Algorithmic bias |
|
Digital divide |
|
Surveillance capitalism |
|
Internet sovereignty |
|
Dual-use technology |
|
A useful analytical lens: the governance gap
One of the most productive ways to read a technology case study is through the governance gap - the structural mismatch between how fast technology develops and how slowly political and legal frameworks adapt to it
It won't be the right lens for every case, but it has analytical traction on most of them
This gap is what creates the political space in which the topic's central conflicts play out

Technological development
New technologies emerge faster than regulatory frameworks can adapt
Governance gaps allow technology to be used in ways that existing law does not cover
Power concentration
States and corporations with advanced technology gain disproportionate capabilities
Others face surveillance, intellectual property theft or exclusion from digital markets
Information environment shifts
Social media and algorithms reshape how people receive and evaluate information
Disinformation spreads rapidly
Political polarisation deepens
Democratic deliberation is undermined
Security implications
Cyberattacks target critical infrastructure, elections and military systems
Traditional security frameworks are inadequate for threats that cross borders without physical action
Digital inequality
Unequal access to technology persists between and within states
Those without digital access are excluded from economic opportunity, political participation and public services
Backlash and fragmentation
States respond with censorship, internet shutdowns and national digital borders
The global internet fragments into national networks, reducing the free flow of information and deepening geopolitical divides
Current and recent technology challenges
With those concepts and the governance-gap framework in place, the contemporary world presents five major technology challenges that affect states at every level
Cybersecurity
Protecting digital systems, networks and data from hostile attack
Targets include critical infrastructure (power grids, financial systems), government networks and private corporations
State-sponsored cyberattacks blur the line between espionage, sabotage and warfare
E.g. the SolarWinds hack (2020), in which state-linked actors compromised US government and private sector systems
Information warfare and disinformation
The use of technology to spread false information, manipulate public opinion and interfere in political processes
Social media algorithms amplify emotionally engaging content - which is often false or extreme — over accurate but moderate material
Disinformation campaigns have been used to undermine trust in democratic institutions, scientific consensus and electoral outcomes
E.g. the use of social media campaigns to interfere in the 2016 US presidential election
Surveillance and digital authoritarianism
States using technology to monitor and control their populations - including facial recognition, location tracking and social media monitoring
Raises profound human rights concerns about privacy, free expression and political dissent
Democratic states also use surveillance technology, raising questions about accountability and the rule of law
E.g. China's social credit system; AI-powered facial recognition used to surveil the Uyghur minority in Xinjiang; internet shutdowns by authoritarian governments during periods of protest
Artificial intelligence and autonomous systems
AI is transforming decision-making in governance, warfare, policing and employment
Algorithmic bias - AI systems can reproduce and amplify human prejudices, producing discriminatory outcomes at scale
Autonomous weapons raise fundamental questions about accountability when lethal force is exercised without direct human control
The digital divide
Unequal access to digital technology and the internet within and between states
Shapes economic opportunity, political participation and access to public services
The divide operates along lines of wealth, geography, gender and age — and intersects with other forms of inequality
Internet penetration rate by country, 2024
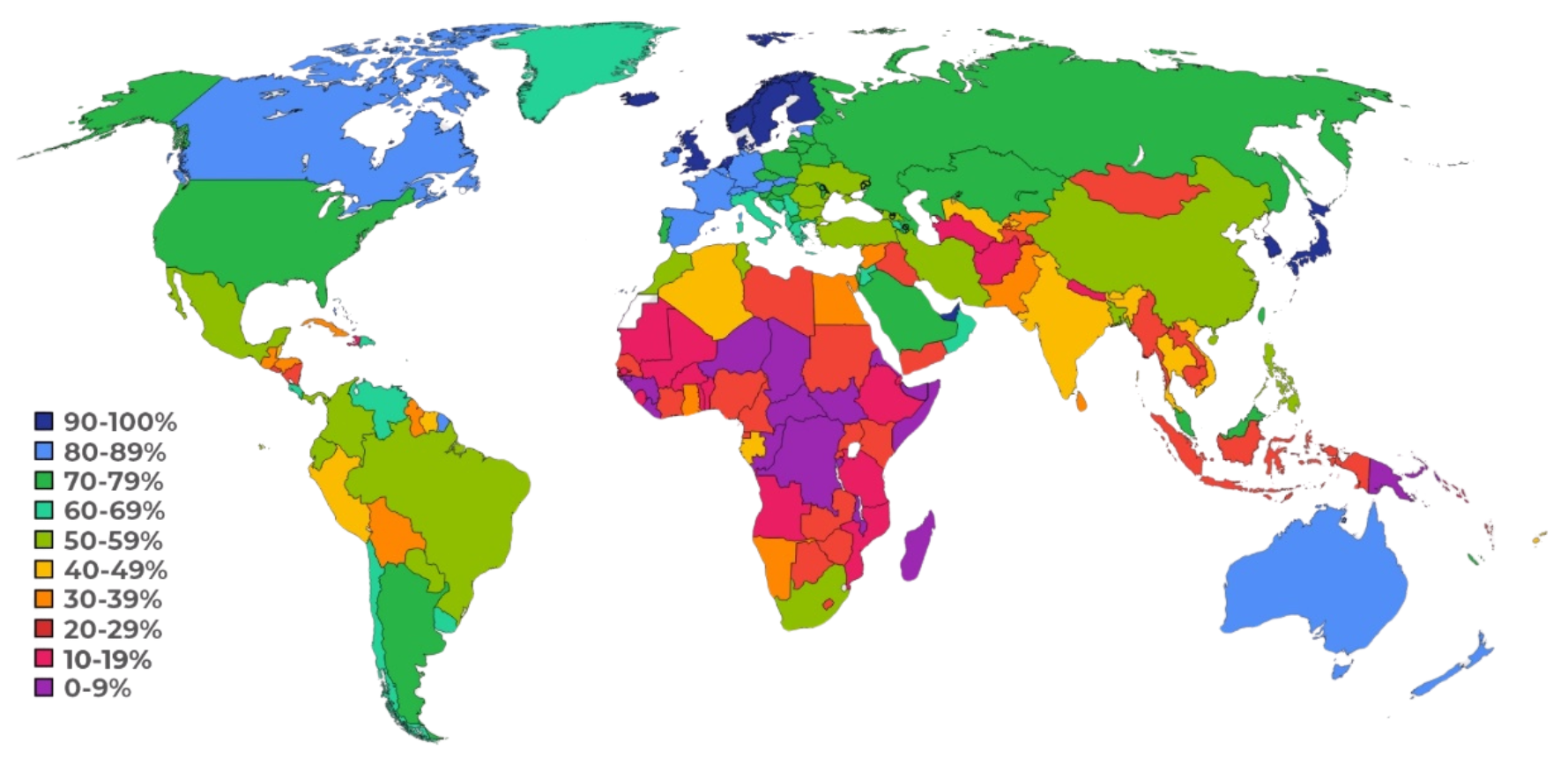
Approximately 63% of people worldwide had reliable access to the internet in 2024, including:
57% of people in the developing world
90% of people in the developed world
Approximately 2.6 billion people remain without internet access globally, concentrated in lower-income states (UN data)
Technology at different levels
Level | Overview |
|---|---|
Global |
|
Regional |
|
National |
|
Local |
|
Actors and stakeholders
When researching a case study on technology, students should identify a range of actors and stakeholders
Nation-states
Develop offensive and defensive cyber capabilities
Regulate technology within their territory and negotiate international norms
May conduct state-sponsored cyberattacks or disinformation campaigns
Large technology corporations
E.g. Google, Meta, Microsoft and Huawei
Control significant global digital infrastructure and shape information environments through algorithms
Collect and monetise vast amounts of user data; operate across borders with limited international accountability
Hackers and cybercriminal organisations
Non-state actors who conduct cyberattacks for financial gain, political purposes or at the direction of states
The line between independent hackers and state proxies is frequently blurred
Civil society and digital rights organisations
E.g. the Electronic Frontier Foundation and Access Now
Advocate for privacy rights, internet freedom and accountability of technology companies and governments
International organisations
E.g. the UN GGE and the International Telecommunication Union (ITU)
Attempt to develop international norms, standards and agreements for technology governance
Individuals and communities
Both users of technology and subjects of technological surveillance
Rights to privacy, free expression and equal digital access are central to all technology governance debate
Case Study
THE GOVERNANCE OF CYBERSPACE
Cyberspace is often described as the fifth domain of conflict, alongside land, sea, air and space, but it is uniquely difficult to govern
There is currently no comprehensive international treaty governing state behaviour in cyberspace
Key governance challenges
Attribution
It is technically difficult to prove definitively who carried out a cyberattack, allowing states to deny involvement plausibly
Dual-use technology
The same tools used for legitimate cybersecurity research can be weaponised
Differing visions of internet governance
Democratic states generally favour an open, globally connected internet; authoritarian states advocate for internet sovereignty and national control
The role of non-state actors
Major technology corporations (Google, Meta, Microsoft) play significant roles in governing cyberspace, often without democratic accountability
Key developments in cyber governance
The UN Group of Governmental Experts (GGE) has produced consensus reports establishing that international law applies in cyberspace — but states disagree sharply on how
The Budapest Convention on Cybercrime (2001) is the primary international treaty on cybercrime; major powers including Russia and China have not ratified it
The EU's General Data Protection Regulation (GDPR, 2018) is the most significant regional data protection framework and has influenced global standards
Example case studies
The following examples illustrate the kinds of case studies students could develop for this topic area
Case study | Outline | Connections to other HL topics |
|---|---|---|
Cyberattacks and US-China relations |
|
|
Far-right social media and elections in Germany |
|
|
Green technology and development in India |
|
|
Links to earlier course content
The technology topic area connects to all four areas of the IB Global Politics course
Section | Key connections |
|---|---|
Core topics |
|
Rights and justice |
|
Development and sustainability |
|
Peace and conflict |
|
Links to the other HL topic areas
A case study on technology will frequently connect to other HL topic areas - identifying these links is essential for question 3
HL topic area | Key connections |
|---|---|
Security |
|
Equality |
|
Identity |
|
Borders |
|
Poverty |
|
Environment |
|
Examiner Tips and Tricks
What distinguishes top-band answers is the deployment of named analytical concepts rather than description alone.
The governance gap is one strong lens for many technology cases - when applying it, consider how the mismatch between technological development and regulation creates opportunities for state and non-state actors to act with impunity, and ask which actors benefit from weak governance and which are harmed.
The syllabus also rewards drawing on the four core concepts (power, sovereignty, legitimacy, interdependence), broader theoretical perspectives (realism, liberalism, constructivism, critical theory), levels of analysis (local to global) and multiple stakeholder perspectives. The right concept depends on your specific case - and many cases reward more than one.

Unlock more, it's free!
Was this revision note helpful?
